Azure Identity client library for Python — Azure SDK for Python 2.0.0 documentation

David Richardson
Published Feb 16, 2026
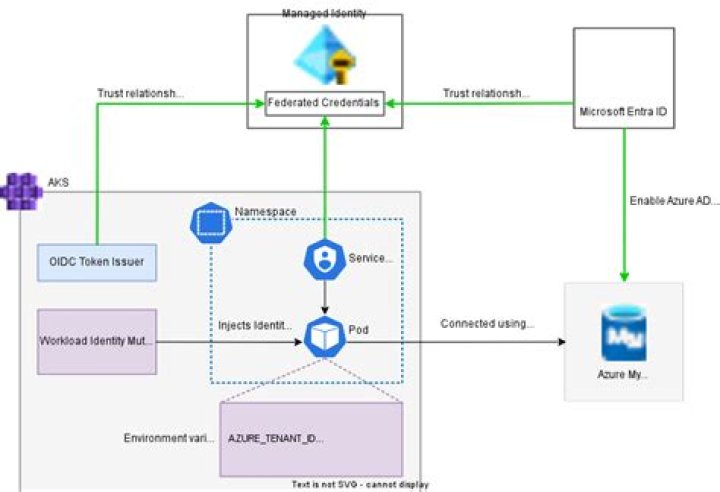
Azure Identity authenticating with Azure Active Directory for Azure SDK libraries. It provides credentials Azure SDK clients can use to authenticate their requests.
This library currently supports:
Prerequisites¶
Install the package¶
Install Azure Identity with pip:
pip install azure-identity
Creating a Service Principal with the Azure CLI¶
This library doesn’t require a service principal, but Azure applications commonly use them for authentication. If you need to create one, you can use this Azure CLI snippet. Before using it, replace “” with a more appropriate name for your service principal.
Create a service principal:
az ad sp create-for-rbac --name --skip-assignment
Example output:
{ "appId": "generated-app-id", "displayName": "app-name", "name": "", "password": "random-password", "tenant": "tenant-id"}
Azure Identity can authenticate as this service principal using its tenant id (“tenant” above), client id (“appId” above), and client secret (“password” above).
Credentials¶
A credential is a class which contains or can obtain the data needed for a service client to authenticate requests. Service clients across the Azure SDK accept credentials as constructor parameters, as described in their documentation. The next steps section below contains a partial list of client libraries accepting Azure Identity credentials.
Credential classes are found in the azure.identity namespace. They differ
in the types of identities they can authenticate as, and in their configuration:
Credentials can be chained together and tried in turn until one succeeds; seechaining credentials for details.
Service principal and managed identity credentials have async equivalents in the azure.identity.aio namespace, supported on Python 3.5.3+. See the async credentials example for details. Async user credentials will be part of a future release.
DefaultAzureCredential¶
DefaultAzureCredential is appropriate for most applications intended to run in Azure. It can authenticate as a service principal, managed identity, or user, and can be configured for local development and production environments without code changes.
To authenticate as a service principal, provide configuration inenvironment variables as described in the next section.
Authenticating as a managed identity requires no configuration but is only possible in a supported hosting environment. See Azure Active Directory’smanaged identity documentationfor more information.
Single sign-on¶
During local development on Windows, DefaultAzureCredentialcan authenticate using a single sign-on shared with Microsoft applications, for
example Visual Studio 2019. This may require additional configuration when
multiple identities have signed in. In that case, set the environment variablesAZURE_USERNAME (typically an email address) and AZURE_TENANT_ID to select
the desired identity. Either, or both, may be set.
Environment variables¶
DefaultAzureCredential andEnvironmentCredential can be configured with environment variables. Each type of authentication requires values for specific variables:
Service principal with secret¶
variable name
value
AZURE_CLIENT_IDid of an Azure Active Directory application
AZURE_TENANT_IDid of the application’s Azure Active Directory tenant
AZURE_CLIENT_SECRETone of the application’s client secrets
Service principal with certificate¶
variable name
value
AZURE_CLIENT_IDid of an Azure Active Directory application
AZURE_TENANT_IDid of the application’s Azure Active Directory tenant
AZURE_CLIENT_CERTIFICATE_PATHpath to a PEM-encoded certificate file including private key (without password protection)
Username and password¶
variable name
value
AZURE_CLIENT_IDid of an Azure Active Directory application
AZURE_USERNAMEa username (usually an email address)
AZURE_PASSWORDthat user’s password
Note: username/password authentication is not supported by the async API (azure.identity.aio)
Configuration is attempted in the above order. For example, if values for a client secret and certificate are both present, the client secret will be used.
Authenticating with DefaultAzureCredential¶
This example demonstrates authenticating the BlobServiceClient from theazure-storage-blob library usingDefaultAzureCredential.
from azure.identity import DefaultAzureCredentialfrom azure.storage.blob import BlobServiceClient# This credential first checks environment variables for configuration as described above.# If environment configuration is incomplete, it will try managed identity.credential = DefaultAzureCredential()client = BlobServiceClient(account_url, credential=credential)
Authenticating a service principal with a client secret:¶
This example demonstrates authenticating the KeyClient from theazure-keyvault-keys library usingClientSecretCredential.
from azure.identity import ClientSecretCredentialfrom azure.keyvault.keys import KeyClientcredential = ClientSecretCredential(tenant_id, client_id, client_secret)client = KeyClient("", credential)
Authenticating a service principal with a certificate:¶
This example demonstrates authenticating the SecretClient from theazure-keyvault-secrets library usingCertificateCredential.
from azure.identity import CertificateCredentialfrom azure.keyvault.secrets import SecretClient# requires a PEM-encoded certificate with private keycert_path = "/app/certs/certificate.pem"credential = CertificateCredential(tenant_id, client_id, cert_path)# if the private key is password protected, provide a 'password' keyword argumentcredential = CertificateCredential(tenant_id, client_id, cert_path, password="cert-password")client = SecretClient("", credential)
Chaining credentials¶
ChainedTokenCredential links multiple credential instances to be tried sequentially when authenticating. It will try each chained credential in turn until one provides a token or fails to authenticate due to an error.
The following example demonstrates creating a credential which will attempt to
authenticate using managed identity, and fall back to a service principal when
managed identity is unavailable. This example uses the EventHubClient from
the azure-eventhub client library.
from azure.eventhub import EventHubClientfrom azure.identity import ChainedTokenCredential, ClientSecretCredential, ManagedIdentityCredentialmanaged_identity = ManagedIdentityCredential()service_principal = ClientSecretCredential(tenant_id, client_id, client_secret)# when an access token is needed, the chain will try each credential in order,# stopping when one provides a token or fails to authenticate due to an errorcredential_chain = ChainedTokenCredential(managed_identity, service_principal)# the ChainedTokenCredential can be used anywhere a credential is requiredclient = EventHubClient(host, event_hub_path, credential_chain)
Async credentials:¶
This library includes an async API supported on Python 3.5+. To use the async credentials in azure.identity.aio, you must first install an async transport, such as aiohttp. Seeazure-core documentationfor more information.
Async credentials should be closed when they’re no longer needed. Each async
credential is an async context manager and defines an async close method. For
example:
from azure.identity.aio import DefaultAzureCredential# call close when the credential is no longer neededcredential = DefaultAzureCredential()...await credential.close()# alternatively, use the credential as an async context managercredential = DefaultAzureCredential()async with credential: ...
This example demonstrates authenticating the asynchronous SecretClient fromazure-keyvault-secrets with an asynchronous
credential.
# most credentials have async equivalents supported on Python 3.5.3+from azure.identity.aio import DefaultAzureCredentialfrom azure.keyvault.secrets.aio import SecretClient# async credentials have the same API and configuration as their synchronous# counterparts, and are used with (async) Azure SDK clients in the same waydefault_credential = DefaultAzureCredential()client = SecretClient("", default_credential)
General¶
Credentials raise CredentialUnavailableError when they’re unable to attempt
authentication because they lack required data or state. For example,EnvironmentCredential will raise this exception whenits configuration is incomplete.
Credentials raise azure.core.exceptions.ClientAuthenticationError when they fail
to authenticate. ClientAuthenticationError has a message attribute which
describes why authentication failed. When raised byDefaultAzureCredential or ChainedTokenCredential,
the message collects error messages from each credential in the chain.
For more details on handling Azure Active Directory errors please refer to the Azure Active Directoryerror code documentation.
Client library support¶
This is an incomplete list of client libraries accepting Azure Identity credentials. You can learn more about these libraries, and find additional documentation of them, at the links below.
Provide Feedback¶
If you encounter bugs or have suggestions, pleaseopen an issue.
This project welcomes contributions and suggestions. Most contributions require you to agree to a Contributor License Agreement (CLA) declaring that you have the right to, and actually do, grant us the rights to use your contribution. For details, visit .
When you submit a pull request, a CLA-bot will automatically determine whether you need to provide a CLA and decorate the PR appropriately (e.g., label, comment). Simply follow the instructions provided by the bot. You will only need to do this once across all repos using our CLA.
This project has adopted theMicrosoft Open Source Code of Conduct. For more information, see theCode of Conduct FAQor contact opencode@microsoft.com with any additional questions or comments.
Indices and tables¶
Developer Documentation